July 19, 2018 – Researchers at Dartmouth College have created a fix to the Spectre computer hardware vulnerability using ELFbac policy techniques. This is the first mechanism of its kind to comprehensively protect against the “Variant 1” form of Spectre.
The solution developed at Dartmouth uses ELFbac to securely partition a program’s address space. This approach ensures that all data and code – including user secrets – are isolated from each other. The ELFbac policy approach denies access to Spectre and results in processing that is generally more secure.
Spectre and its companion vulnerability, Meltdown, were revealed to the public earlier this year, calling into question the security of information contained on computer processors that run in just about every chip-based device including computers, phones and tablets. Spectre has three different versions – called “variants” – that have been identified by researchers.
The exploit attacks the tendency of software to place data secrets alongside less important information within the same program. While this approach can optimize computer performance, it can also unintentionally facilitate data compromise because all of a program’s information is made available to all components within that same program, even untrusted third party libraries.
“A program should not allow components containing sensitive information to interact with other elements of the software,” said Ira Ray Jenkins, a PhD student at Dartmouth and a member of the research team. “The ELFbac mechanism protects against compromises that violate the constraints the programmer implicitly intended.”
Spectre specifically focuses on the so-called “speculative execution” that constantly runs on computer processors. This procedure – akin to the software guessing what actions it should take next in order to speed up computer processing – can leave sensitive information in the computer’s cache during normal operations.
Spectre hitches a ride into the shared space of the cache and exposes data when the processor should be clearing personal user information or secure computer processing information after a speculative execution. This can compromise information like passwords or secret encryption keys that are temporarily stored in the shared space.
It would take a sophisticated hacker who knows how to gain access to a target machine to exploit Spectre. While there are no known cases of Spectre Variant 1 being used in an attack, proofs-of-concept do exist and it is estimated that billions of machines are vulnerable to the attack.
“Everyone should feel vulnerable to Spectre,” said Prashant Anantharaman, also a PhD student at Dartmouth who worked on the research team. “A hacker using the exploit could do anything from steal personal passwords to get control of critical infrastructure like a power system.”
Because systems do not distinguish between categories of information, Spectre Variant 1 can trick software into sharing secret information. ELFbac solves Spectre Variant 1 by ensuring that data does not have read or write access after a certain point of time in a program. Even in speculative execution, the program can never read it.
“ELFbac isolates secret information and only makes it available to authorized software when it is required. Without ELFbac, this kind of separation within a single program is very difficult to achieve,” said Jenkins.
The ELFbac software was pioneered at Dartmouth’s TrustLab in 2012 in order to prevent large classes of cyber-attacks that could expose sensitive information. The Dartmouth research team began the effort to use ELFbac against Variant 1 shortly after Spectre was revealed in January of this year.
According to the Dartmouth team, Spectre never works with ELFbac. The effectiveness of ELFbac against this vulnerability demonstrates the significance of looking at using the ELFbac approach for a wider range of security applications.
ELFbac could be useful in systems that need to protect critical data including certificates and private keys in websites. In addition to preventing Spectre, ELFbac has also been used to successfully mitigate the 2016 “Roaming Bug” that used servers to steal private credentials.
“The success we’ve had using ELFbac to secure data is exciting and demonstrates the wide potential of this policy mechanism. Spectre is just one high-profile example of what you can do with ELFbac,” said Sean Smith, a professor of computer science at Dartmouth and advisor to the research team.
Dartmouth College has a long history of innovation in computer science. The term “artificial intelligence” was coined at Dartmouth during a 1956 conference that created the AI research discipline. Other advancements include the design of BASIC -- the first general-purpose and accessible programing language -- and the Dartmouth Time-Sharing System that contributed to the modern day operating system.
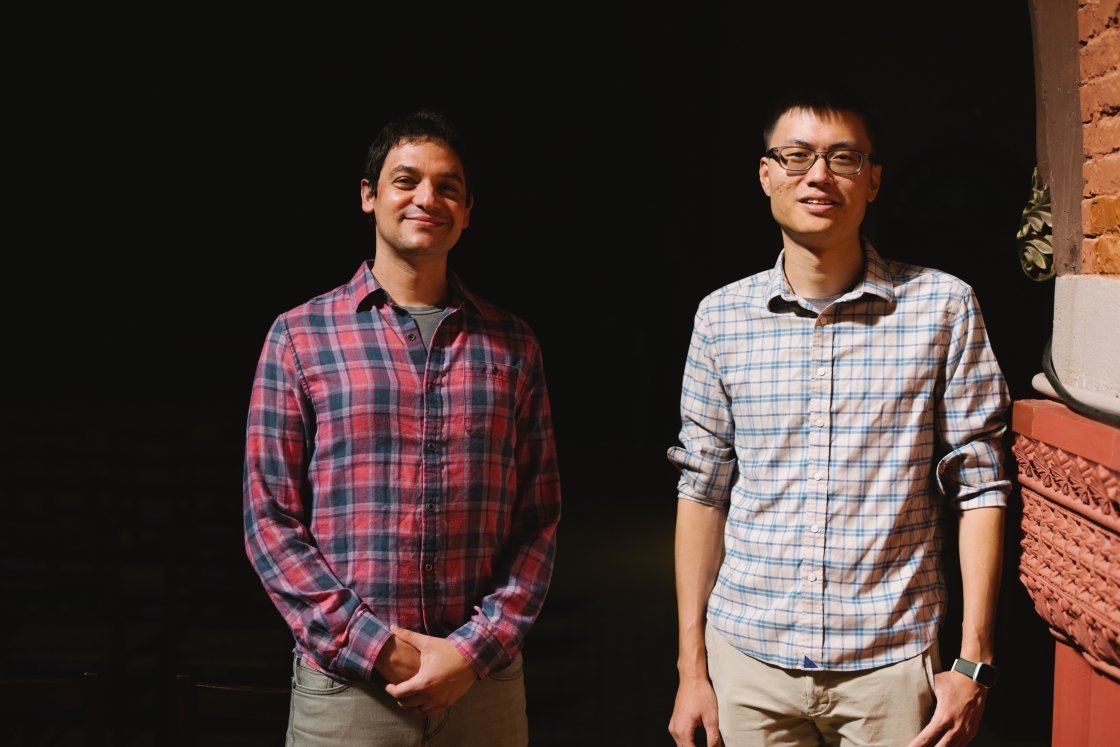
The research on using ELFbac against Spectre was conducted by Dartmouth PhD Students Ira Ray Jenkins and Prashant Anantharaman as well as recent PhD graduate Rebecca Shapiro.